Blog

THC Seltzers: A Versatile Ingredient in Cooking and Baking ltzers: A Versatile Ingredient in Cooking and Baking
In recent years, the landscape of cannabis consumption has undergone a profound transformation. Traditional methods like smoking or vaping are no longer the sole avenues for experiencing the benefits of cannabis. With

Exploring the Intersection of Technology and Online Gaming
In recent years, the evolution of technology has dramatically reshaped numerous industries, with the online gaming sector experiencing one of the most significant transformations. As technology advances, it’s fascinating to delve into

5 Tips for Choosing the Right Internet Service Provider for You
In today’s digital age, the internet has become an essential part of our daily lives, whether it’s for work, entertainment, or staying connected with others. Choosing the right internet service provider (ISP)

Building Your Online Presence: How a Website Builder Can Help
In the ever-evolving digital landscape, having a robust online presence is crucial for success, whether you’re a budding entrepreneur, a seasoned blogger like the team at The Hacker Chick Blog, or a
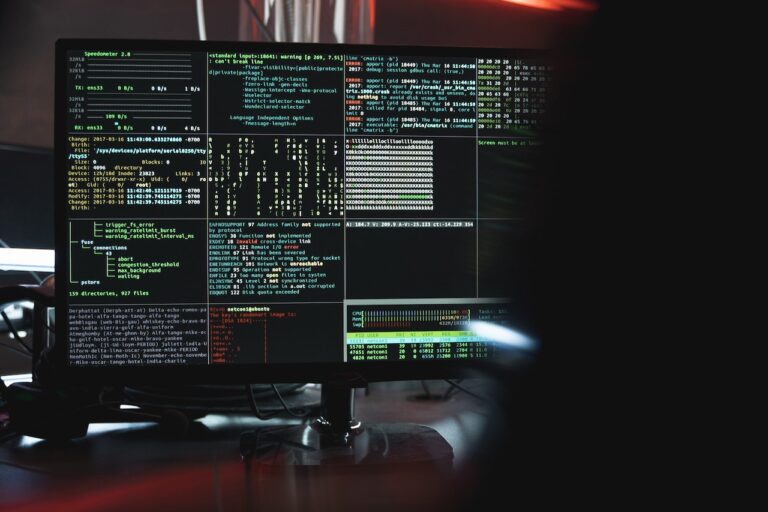
Penetration Testing for SMEs: Fortifying Cybersecurity on a Budget
In today’s interconnected world, Small and Medium-sized Enterprises (SMEs) play a crucial part in the international economy. They are comprehended for their invention, adaptability, and entrepreneurial spirit. However, SMEs face many challenges,

How to Ensure API User Authentication for Your Business
API user authentication is an essential part of securing digital infrastructure for businesses. It is a process that verifies a user’s identity and allows them to access applications or services using their credentials.

Ensuring your stream stays up – no matter what happens
Streaming is big business. According to steamscheme, the top 100 Twitch streamers make at least $32k a month. For the most part, things go smoothly for these people. Typically, they have been
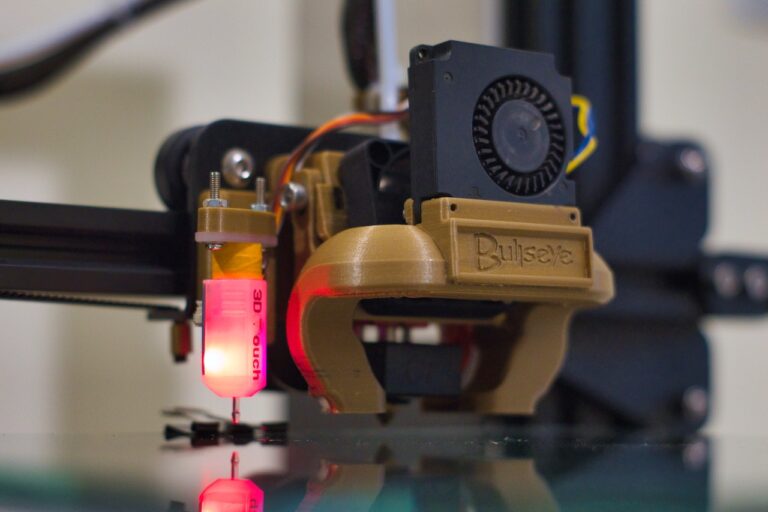
Future Technology – A Primer
This article covers future technologies that will be common in our daily lives. These technologies include 3D printing, Regenerative medicine, and Autonomous devices that will replace humans in many tasks. In addition,

How to Get the Most Out of Technology Product Reviews
Technology product reviews can be invaluable resources for small business owners. These sites provide an index of reviews that can be used to make purchasing decisions. They vary in length, tone, and

Here are All The Prerequisites You Need Before Getting Started With Your Cyber Security Career
Never before has the security and privacy of our data been more crucial. With so much of our information stored persistently online, the fear of data theft is always present. The news

All You Wanted to Know About Moon Landings
Moon landing refers to the landing of manned spacecraft on the moon. These are spacecrafts with people on them that landed on the moon. Of course, we will always remember the first

Earning Online With Website Themes
In the same way that app developers are, website development is always in demand, since businesses are always looking to update and enhance their websites in order to generate more sales. The